Botnet is a network of private computers infected with malicious software and controlled as a group without the owners' knowledge, e.g., to send spam messages....
The onset of the attack techniques in today's technology, one of the most important botnet attacks that .. In general, considering the, is a type of malicious software is hard-coded .. The backbone of DDoS attacks....Determined to attack on an address code is a set of integrated .. But it is more dangerous than a normal ddos attack.
If the features of the sort used briefly threatening situations;
* Thanks to Web addresses via pop-up allows you to advertise an address can also, in general, is a method used by companies in order to promote ..
* Virus, Logger, and so on. may contain malicious software, computer users, their passwords, 2 information disclosure allows parties to be shared ..
* Infect computer networks, data from all the computers on the network share it, so that it becomes overrun Information Security ..
* Spam providing for the use of the e-mails out of the circulation of annoying advertising allows mails ..
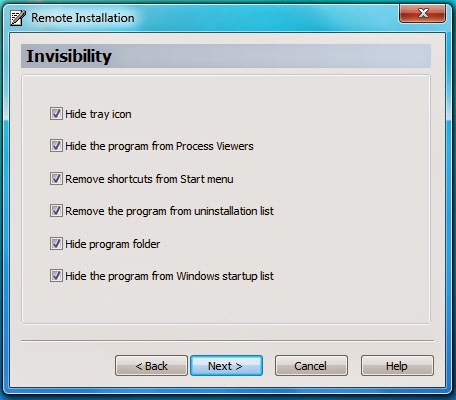
Lined up against the user can cause this and similar methods.. In todaSyC'RsO tLeL cMhE nBoAlCoKg TyO, T HaEn T OoPr.dinary internet users; botnet network installation has become inevitable, namely MP3s downloaded from on the internet,
wallpaper, screensaver, videos, software programs, etc.. before you start on a small scale by a simple code that hackers can then be integrated as a result of the spread of this data allows for botnet which has become a huge mass.
One of the uses of botnet Mirc scripts, this is a huge botnet on chat systems, and where there is a huge virtual world without being aware of net users started to play the role of hooked fish ..
Hang bait, you're aware of the botnet ddos attack on any channel is found set by the owner, advertising messages on the servers will result in the desired
server, the port is added to the desired number of boats to attack .. In addition
to these without being aware of the internet browser, Login ID, except that
consent has changed their set, and the right to make changes in the Options
section of your hand is already taken ..
When you restart the computer, boot your system back up and running again,
and will continue to see the activity on the server ..
Engelleyemeyeceğinizi's worth noting that this type of attack 100%, but this
kind of attack must be taken to protect you, to take steps in this regard can
make a few;
* Continuous updating the computer, the operating system's latest version
şekillendirmelisiniz ..
* If your system updates itself, and the use of frequent difficulty of not going
down, filter, use an antivirus program high ..